内网信息收集清单
"渗透测试的本质是信息收集"
"此篇文章用作介绍拿到Webshell之后的一些针对内网的操作,不包含对域控的信息收集,目的是将主机信息收集最大化,从而加大横向的力度"
内网信息描述
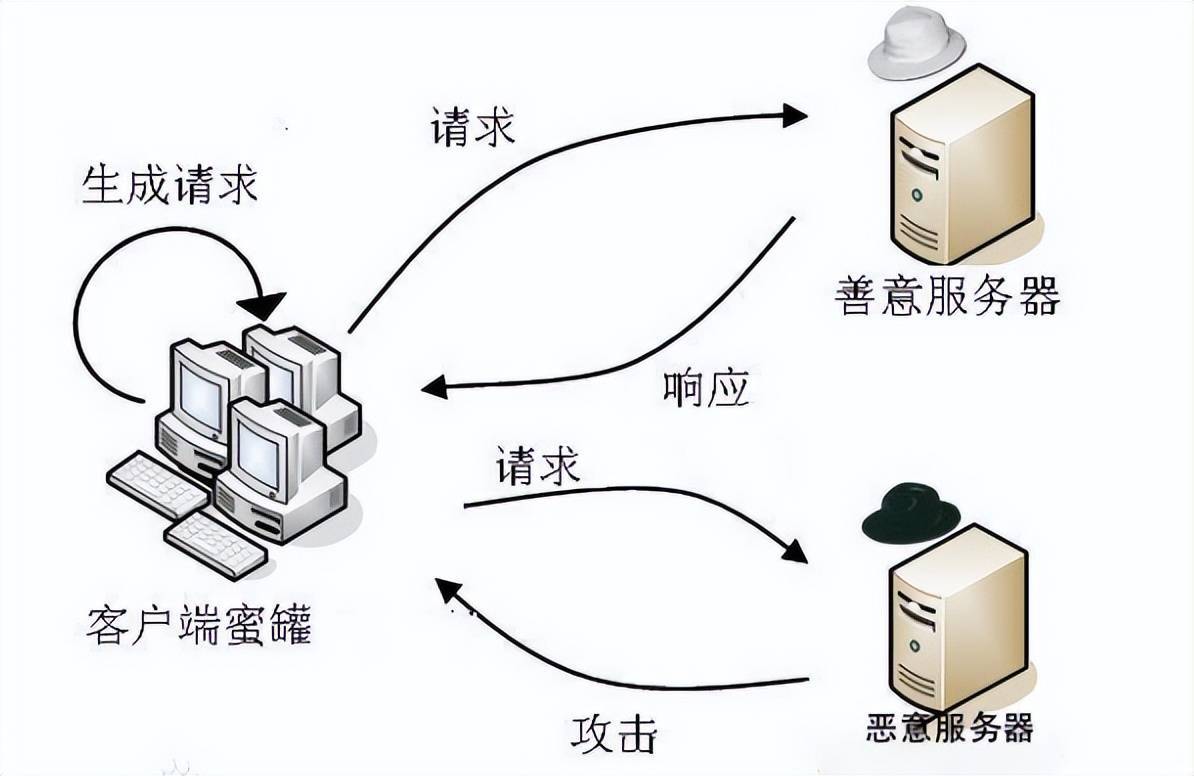
当从Web端拿到webshell之后,对服务器主机的了解几乎是0,应从内往外一步步的收集服务器的相关信息,首先要对主机当前所处的网络环境进行判断,通常来说分为3种:
- 我是谁 对机器角色的判断,是指判断已经控制的机器是 普通Web服务器、开发测试服务器、公共服务器、文件服务器、代理服务器、DNS服务器还是存储服务器等。具体的判断是通过对机器内的 主机名、文件、网络连接等多种情况综合进行的
- 这是哪 对目前机器所处网络环境的拓扑结构进行分析和判断,是指需要对所处内网进行全面的数据收集及分析整理,绘制出大概的内网整体拓扑结构图,以便后期进行进一步的内网渗透和准确定位内网具体目标,从而完成渗透测试
- 我在哪 对目前机器所处位置区域的判断,是指判断机器处于网络拓扑中的哪个区域,是在 **DMZ区、办公网,还是核心区核心DB **等位置。当然,这里的区域并不是绝对的,只是一个大概的环境,不同位置的网络环境不一样,区域的界限也不一定明显
存活主机检测
方法一:
for /l %i in (1,1,255) do @ ping 172.16.80.%i -w 1 -n 1|find /i "ttl="
方法二:
@echo
md C:windowsTemp1
echo ok > C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 192.168.%%I.1 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 10.%%I.1.1 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 172.16.%%I.1 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 172.%%I.1.1 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping %%I.%%I.%%I.1 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 192.168.%%I.254 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 10.%%I.1.254 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 172.16.%%I.254 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping 172.%%I.254.254 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
FOR /L %%I in (1,1,254) do ping %%I.%%I.%%I.254 -n 1 -w 10 | findstr "TTL">>C:WindowsTemp1gatway.txt
方法三:
@echo off
rem 内网存活段自动发现脚本 [Windows]
setlocal enabledelayedexpansion
for /l %%i in (0,1,255) do (
for /l %%k in (0,1,255) do (
ping -w 1 -n 1 10.%%i.%%k.1 | findstr "TTL=" >nul || ping -w 1 -n 1 10.%%i.%%k.254 | findstr "TTL=" >nul
if !errorlevel! equ 0 (echo 10.%%i.%%k.0/24 is alive ! >> alive.txt ) else (echo 10.%%i.%%k.0/24 May be sleeping ! )
)
)
for /l %%s in (16,1,31) do (
for /l %%d in (0,1,255) do (
ping -n 1 -w 1 172.%%s.%%d.1 | findstr "TTL=" >nul || ping -w 1 -n 1 172.%%s.%%d.254 | findstr "TTL=" >nul
if !errorlevel! equ 0 (echo 172.%%s.%%d.0/24 is alive ! >> alive.txt ) else (echo 172.%%s.%%d.0/24 May be sleeping ! )
)
)
for /l %%t in (0,1,255) do (
ping -n 1 -w 1 192.168.%%t.1 | findstr "TTL=" >nul || ping -n 1 -w 1 192.168.%%t.254 | findstr "TTL=" >nul
if !errorlevel! equ 0 (echo 192.168.%%t.0/24 is alive ! >> alive.txt ) else (echo 192.168.%%t.0/24 May be sleeping ! )
)
方法四:powershell
$ip = "172.20.10."
for ($i = 1; $i -lt 255; $i ++){
# get each ip
$cur = $ip + $i
# ping once
ping -n 1 $cur | Out-Null
if ($LASTEXITCODE -eq 0) {
Write-Host "$cur online"
} else {
Write-Host "$cur dead"
}
}
开放端口检测
1.PowerShell端口扫描器:针对单个IP的多个端口的扫描
1..1024 | % {echo ((new-object.NET.Sockets.TcpClient).Connect("172.20.10.1",$_)) "Port $_ is open!"} 2>$null
2.Test-Netconnection 针对某IP段中单个端口的扫描
foreach ($ip in 1..20) {Test-NetConnection -Port 80 -InformationLevel "Detailed" 172.20.10.$ip}
Test-NetConnection命令是在 **4.0 **版本的PowerShell中才引入的。
3.针对某IP段 & 多个端口的扫描器
1..20 | % { $a = $_; 1..1024 | % {echo ((new-object Net.Sockets.TcpClient).Connect("172.20.10.$a",$_)) "Port $_ is open!"} 2>$null}
4.针对某IP段 & 指定多个端口的扫描器
1..20 | % { $a = $_; write-host "------"; write-host "172.20.10.$a"; 22,53,80,445 | % {echo ((new-object Net.Sockets.TcpClient).Connect("10.0.0.$a",$_)) "Port $_ is open!"} 2>$null}
常见的端口及服务
21、69FTPTFTP弱口令嗅探22SSH弱口令23telnet弱口令、嗅探、探测25SMTP邮件53DNS区域传送、dns欺骗、域控67、68DHCP劫持、欺骗80、443、8080WEB应用弱口令、WEB攻击7001、7002weblogic反序列化、弱口令8080、8089jboss、jenkins反序列化、弱口令9090websphere反序列化、弱口令110POP3爆破、嗅探139、445samba未授权访问、远程代码执行143IMAP爆破161SNMP爆破、信息泄露389LDAP弱口令、匿名访问3389RDP爆破、远程代码执行5900VNC弱口令5632PcAnywhere嗅探、代码执行3306MySQL弱口令1433msssql、sql server弱口令1521oracle弱口令5432pgsql弱口令27017、27018mongodb未授权访问6379redis未授权访问5000sysbase/DB2弱口令11211memcached未授权访问9200、9300elasticsearch远程代码执行2181zookeeper未授权访问8069zabbix远程执行3690SVNSVN泄露873rsync匿名访问888、8888宝塔宝塔后门、弱口令
系统信息
wmic OS get Caption,CSDVersion,OSArchitecture,Version!
用户信息
whoami/all
query user
whoami/user
whoami/priv
补丁信息
systeminfo 查看KB号
wmic qfe get Caption,Description,HotFixID,InstalledOn 查看安装的补丁 提权辅助网页
根据补丁查找exp http://bugs.hacking8.com/tiquan/
DNS
DNS服务器:nslookup
DNS缓存:ipconfig /displaydns
host文件
type c:Windowssystem32driversetchosts
敏感文件
dir /a /s /b d:"*.txt"
dir /a /s /b d:"*.xml"
dir /a /s /b d:"*.mdb"
dir /a /s /b d:"*.sql"
dir /a /s /b d:"*.mdf"
dir /a /s /b d:"*.eml"
dir /a /s /b d:"*.pst"
dir /a /s /b d:"*conf*"
dir /a /s /b d:"*bak*"
dir /a /s /b d:"*pwd*"
dir /a /s /b d:"*pass*"
dir /a /s /b d:"*login*"
dir /a /s /b d:"*user*"
网络环境
ipconfig /all
netstat -ano
arp -a
route print
tracert
Tomcat、Nginx、Apache、web.config等配置文件
进程信息
可以查看进程是否有 mysql,nginx,Apache,redis等敏感服务tasklist /svc or wmic process list brief进程杀软对比工具-avlist https://github.com/gh0stkey/avList/
服务信息
wmic service list brief查看是否开启DHCP或其他第三方服务
已安装程序
wmic product get name,version
powershell "Get-WmiObject -class Win32_Product |Select-Object -Property name,version
查看已安装程序,判断机器作用及价值,如安装了VMware vSphere Client或者xshell,ftp等,就可以去提取账号口令了
本地运行环境
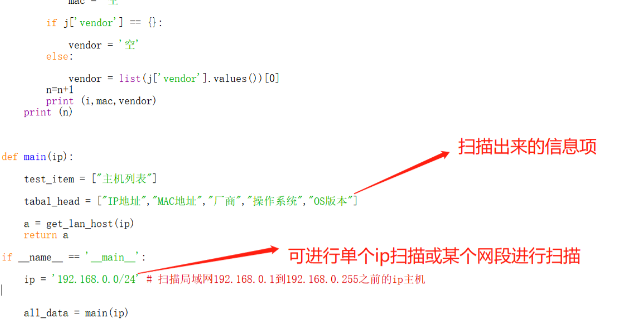
set 这个没什么好说的,看看主机有无JAVA,Perl,Python/ target=_blank class=infotextkey>Python等环境,尽可能的收集信息
计划任务
schtasks /query
开机时间
启动项信息
wmic startup get command,caption
REG QUERY HKEY_CURRENT_USERSOFTWAREMicrosoftWindowsCurrentVersionRun
REG QUERY HKEY_LOCAL_macHINESOFTWAREMicrosoftWindowsCurrentVersionRun
RDP连接日志
cmdkey /list
防火墙配置
netsh advfirewall show allprofiles
最近打开文件
C:Users[User]AppDataRoamingMicrosoftWindowsRecent
回收站
软件敏感信息
list
- 浏览器下载记录
- 浏览器历史记录
- 浏览器保存的账号密码
- 浏览器收藏夹标签
Github项目
https://github.com/GhostPack/Seatbelt 爬取浏览器收藏夹等机器其他敏感资产https://github.com/moonD4rk/HackBrowserData hackbrowserdata 是一个解密浏览器数据(密码|历史记录|Cookies|书签)的导出工具,支持全平台主流浏览器https://github.com/AlessandroZ/LaZagne LaZagne项目是用于开源应用程序获取大量的密码存储在本地计算机上
文章转自公众号TIDE安全团队